Smart Technology Investments: Avoiding Traps and Maximizing Returns in 2024 In the relentless race to stay competitive, businesses often turn to a dazzling array of new technologies with promises of productivity boosts and increased profits. However, the path to successful technology investment is riddled with hidden costs and unexpected setbacks. This isn't to say tech […]
Windows 11, Microsoft's latest operating system, comes packed with an array of security features. However, to fully harness its capabilities, reviewing and activating specific settings is essential. This guide will help you optimize your Windows 11 security for maximum protection. Discover the secrets to unlocking unbeatable security on your Windows 11 system with our comprehensive […]
As the modern workplace evolves, businesses must adapt to the changing landscape by embracing remote work and allowing employees to complete tasks from anywhere. Dell Technologies is at the forefront of this change, offering a suite of hardware and software solutions designed to meet the unique needs of today's workforce.
Hey there, tech enthusiasts! If you're searching for a laptop that oozes style and sophistication without compromising performance, look no further than the Microsoft Surface Laptop 5 15. We're here to give you the lowdown on this sleek machine, from its eye-catching design to its powerful capabilities.
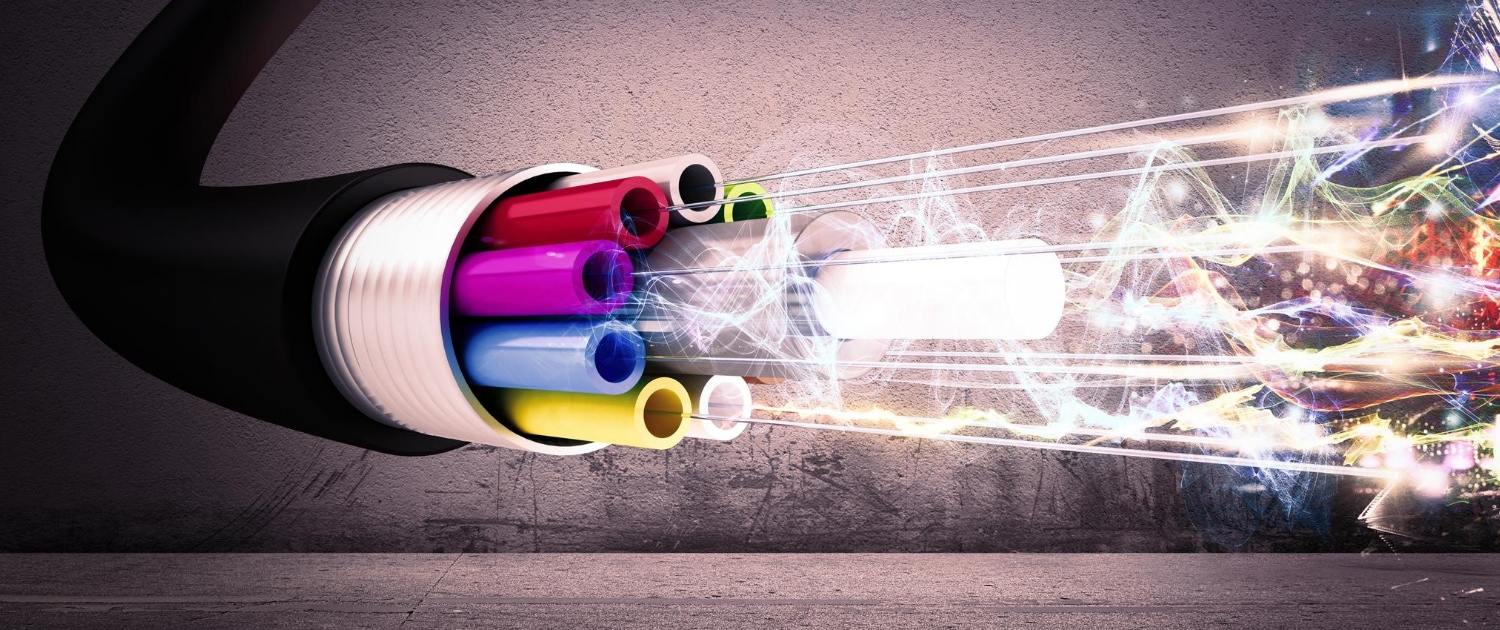
AT&T Business Fiber has emerged as a top choice for Miami businesses searching for ultra-fast internet speeds, reliable connectivity, and outstanding value with its 1 GIG package. This article will delve into the features, advantages, disadvantages, and pricing of AT&T Business Fiber's various offerings while shedding light on real-life experiences with their services.
Step into a world where digital transformation takes center stage, reshaping how we do business. As the digital landscape continuously evolves, companies must swiftly adapt to new technologies to remain at the forefront of innovation. Dive into this guide with essential IT tools and resources to catapult your small business into a future filled with […]
In the age of technology, small businesses need the right tools to stay ahead of the competition. This guide lists some of the best small business tools to help streamline your operations, boost your company's productivity, and enhance security.
Wi-Fi Sensing is a transformative technology that uses existing Wi-Fi infrastructure's radio frequency (RF) signals to detect presence and motion. Beyond transmitting data, this innovation enables sensing capabilities with potential applications in healthcare, security, home automation, and beyond. With advancements in Wi-Fi standards, Wi-Fi Sensing is poised to become an integral component of smart living, […]
Google has recently announced plans to integrate artificial intelligence (AI) into its widely-used Google Workspace platform, including Gmail. This groundbreaking innovation is set to reshape how users interact with email, collaborate on documents, and create presentations.
Generative capabilities are making their way into the world of business applications, and Microsoft is joining the trend. In response to Google's recent announcement about adding generative AI tools to its popular productivity products, Microsoft has revealed its plans to integrate Copilot 365 enhancements into its Microsoft 365 Business software suite. The Redmond-based company aims […]