Why Two-Factor Authentication Is a Must for Online Account Security
Last Updated on October 13, 2022
Two-factor authentication has become a necessity for online security. By adding an extra layer of protection, businesses and individuals can ensure that their accounts are more secure against unauthorized access.
Every business, from the smallest startup to the largest corporation, is at risk if they do not take steps to protect its devices and data.
Cyber attacks are no longer random events but deliberate attempts by professional criminals to generate revenue.
Most people became familiar with two-step verification when they began banking online. For years now, after entering their password, we have had to input a unique code received via SMS to access their bank account.
Multi-Factor authentication is now required by services ranging from social media platforms to corporate telework systems, which is excellent news for security professionals and end users.
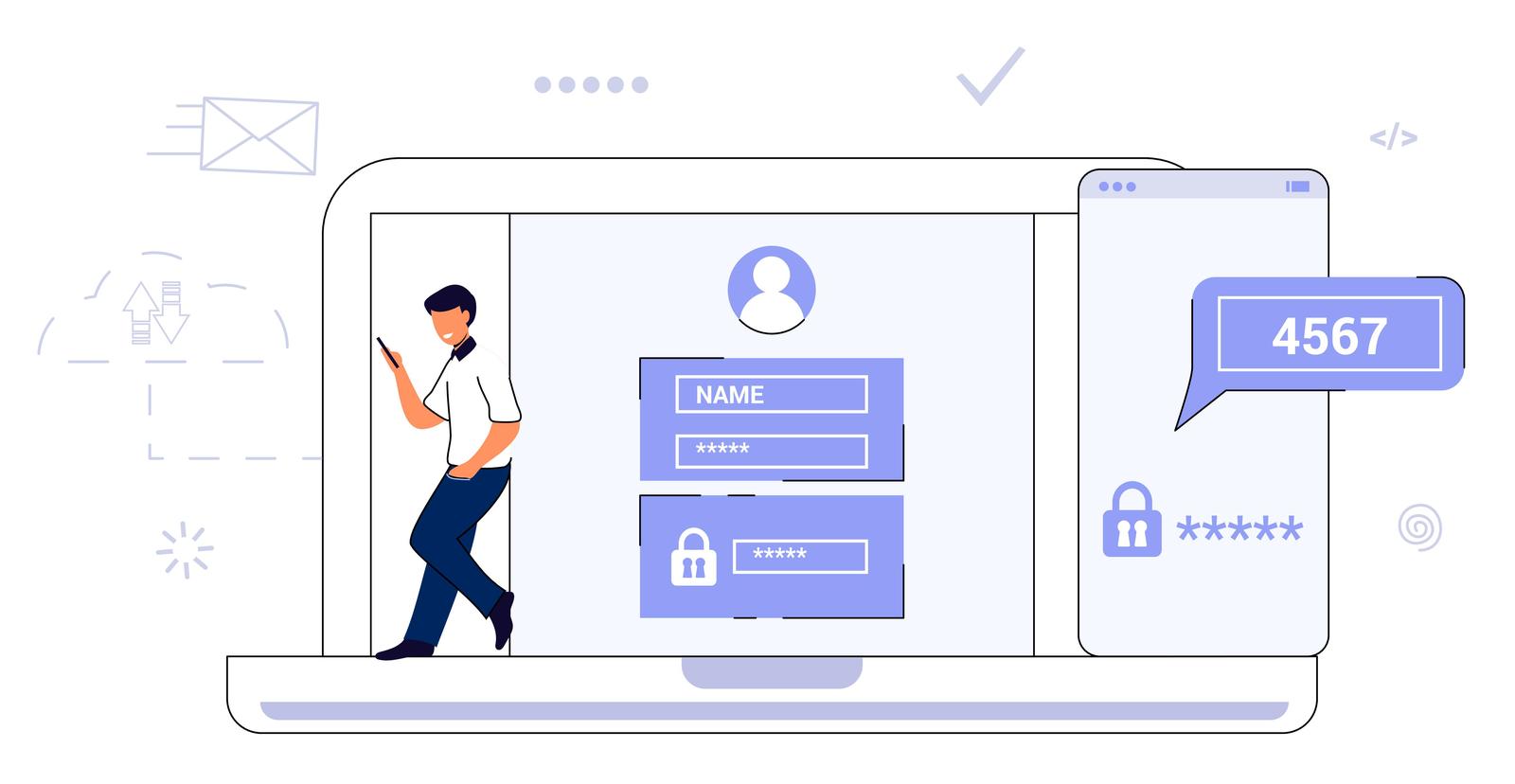
Table of Contents
The Password Dilemma
A password that is easy to remember is also easy to guess. Contrarily, a password that is difficult to remember presents its own challenges.
It can be difficult to remember long, senseless strings of characters that include both upper and lower-case letters, numbers, and special symbols. As a result, many people resort to writing them down on paper or saving them to an unprotected text file on their computer, which is a big problem.
Storing Passwords
A password written down on paper in an office is difficult for a cybercriminal from another country to access – however, someone with physical access to the office would have a much easier time getting it.
The risks are reversed regarding passwords stored on a computer or online service. While secure password management services are an excellent way of storing sensitive information, software vulnerabilities can be a problem.
Password Managers
Password manager software is essential for many reasons. First, they can help you keep track of your passwords, making it easier to remember and stay organized. Additionally, password manager software provides an extra layer of security to keep your passwords encrypted and safe.
A password manager can also help create strong, unique passwords for each account, making it much harder for hackers to tamper with your online accounts.
Multi-Factor Authentication
The most effective solution currently is two-step authentication, also known as multi-factor authentication. The term itself is pretty descriptive of what it is: in addition to the usual “secret code” (password), one (or more) additional steps are required for the system to be accessed.
IT professionals believe keeping operating systems and software updated and implementing multi-factor authentication can protect against 99% of known attacks.
Beyond SMS
Authenticator apps are becoming increasingly popular, especially in corporate environments, as they are more convenient than SMS or email, which can often take a while to arrive.
The most popular authenticators are Google Authenticator and Microsoft Authenticator. These can be used to add compatible services, which generate one-time codes that are valid for a few seconds and continuously change.
Biometrics
The second step in authentication does not have to be an SMS or an authenticator app. With the increasing popularity of smartphones with biometric identification capabilities, it is reasonable to expect that employees can use a fingerprint reader or facial recognition on their mobile devices.
As the cybersecurity industry continues to evolve, more and more professionals are beginning to see biometric identification as a robust enough security measure to stand on its own without the need for a password.
The Future
Fido Alliance is a non-profit organization that promotes interoperability and security standards for the authentication of devices and services. The technology of Fido is based on an open architecture that allows for any service or device to be securely authenticated using a Fido-compliant security key.
The Fido Alliance's security key standard gives users more choice and control over their online identities, helping to reduce reliance on passwords. Fido-compliant security keys are available in various form factors, including USB, NFC, and Bluetooth.
Apple, Google, and Microsoft now support the Fido Alliance's technology. The simplest way to use the Fido-compatible system is with a modern smartphone, which already has a fingerprint reader and camera that are advanced enough to provide high-level security.
This can quickly lead to the point where, within a few years, we no longer have to endure the inconvenience of multi-factor authentication and can say goodbye to our passwords.







Leave a Reply
Want to join the discussion?Feel free to contribute!